People downloaded this tool to keep their passwords safe
But it had a major flaw
Advertisement
Read this article for free:
or
Already have an account? Log in here »
To continue reading, please subscribe:
Monthly Digital Subscription
$1 per week for 24 weeks*
- Enjoy unlimited reading on winnipegfreepress.com
- Read the E-Edition, our digital replica newspaper
- Access News Break, our award-winning app
- Play interactive puzzles
*Billed as $4.00 plus GST every four weeks. After 24 weeks, price increases to the regular rate of $19.95 plus GST every four weeks. Offer available to new and qualified returning subscribers only. Cancel any time.
Monthly Digital Subscription
$4.99/week*
- Enjoy unlimited reading on winnipegfreepress.com
- Read the E-Edition, our digital replica newspaper
- Access News Break, our award-winning app
- Play interactive puzzles
*Billed as $19.95 plus GST every four weeks. Cancel any time.
To continue reading, please subscribe:
Add Free Press access to your Brandon Sun subscription for only an additional
$1 for the first 4 weeks*
*Your next subscription payment will increase by $1.00 and you will be charged $16.99 plus GST for four weeks. After four weeks, your payment will increase to $23.99 plus GST every four weeks.
Read unlimited articles for free today:
or
Already have an account? Log in here »
Hey there, time traveller!
This article was published 29/07/2016 (3507 days ago), so information in it may no longer be current.
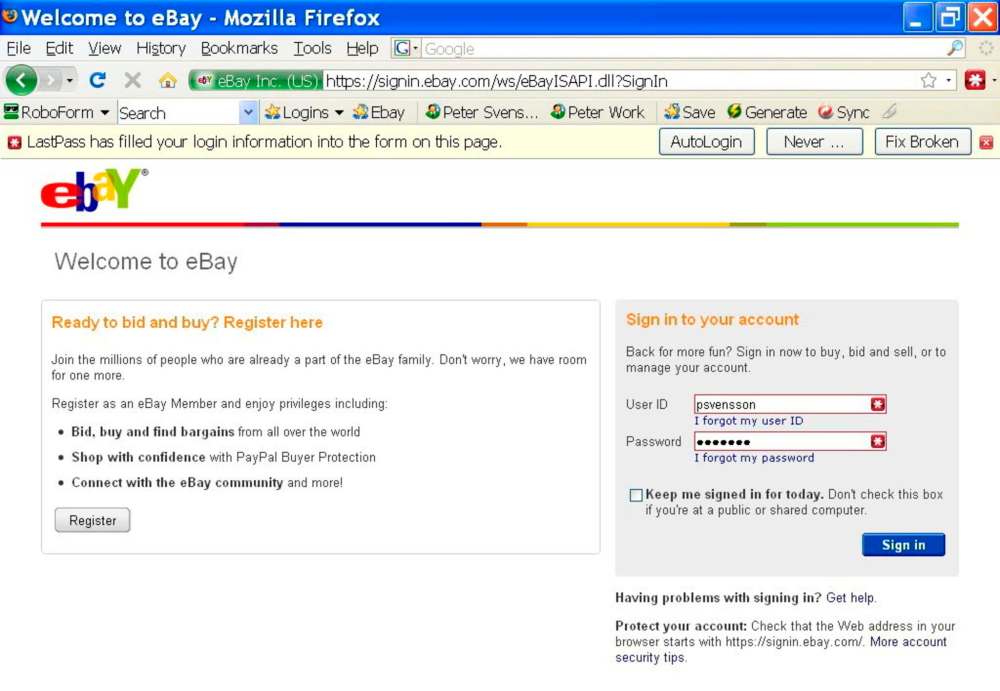
Millions of people count on password managers to safeguard their accounts and help them keep track of their passwords. By serving as a sort of master-key for their accounts, password managers can encourage good digital hygiene, such as using long, complex and unique passwords.
But a major vulnerability in one of the most popular password managers, LastPass, shows how even the tactics users hope will protect them online can still leave them vulnerable — and how just hard it is to keep up with what technology to trust.
Tavis Ormandy, a member of a Google team that hunts for unknown software bugs, discovered the LastPass problem Tuesday — calling it a “complete remote compromise.” A distant attacker could potentially take over users’ LastPass accounts and gain access to their troves of passwords — at least, if they visited a website designed to exploit the vulnerability while using the LastPass browser extension with Firefox, according to a blog post from LastPass.
LastPass pushed out an update Wednesday fixing the problem. At the same time, it also acknowledged an issue that similarly exposed user passwords and was disclosed to LastPass by security researcher Mathias Karlsson last year.
The company fixed the problem Karlsson discovered back when he told them about it, but it wasn’t made public until Wednesday when Karlsson published a blog post explaining the bug. Industry best practice is for researchers to wait until after problems have been fixed to talk about them, but companies don’t always publicly announce when they’ve made major fixes.
This isn’t the first time password managers have had security problems. Back in 2014, researchers uncovered security problems in LastPass and four other password managers. Just last year, researchers were able to sneak a malicious program into the Apple App Store that could steal passwords from iOS and OSX’s built-in Keychain password-management tool, as well as from popular password manager 1Password.
Earlier this week, a government agency also waved developers away from another common account security strategy: using SMS text messages to deliver two-factor authentication codes. Two-factor authentication is one of the best, basic steps people can take to secure their accounts — it works by having a user verify their identity by using another method beyond a password, most often by entering a unique code sent to them via text message.
— Washington Post
History
Updated on Friday, July 29, 2016 7:29 AM CDT: Headline fixed

